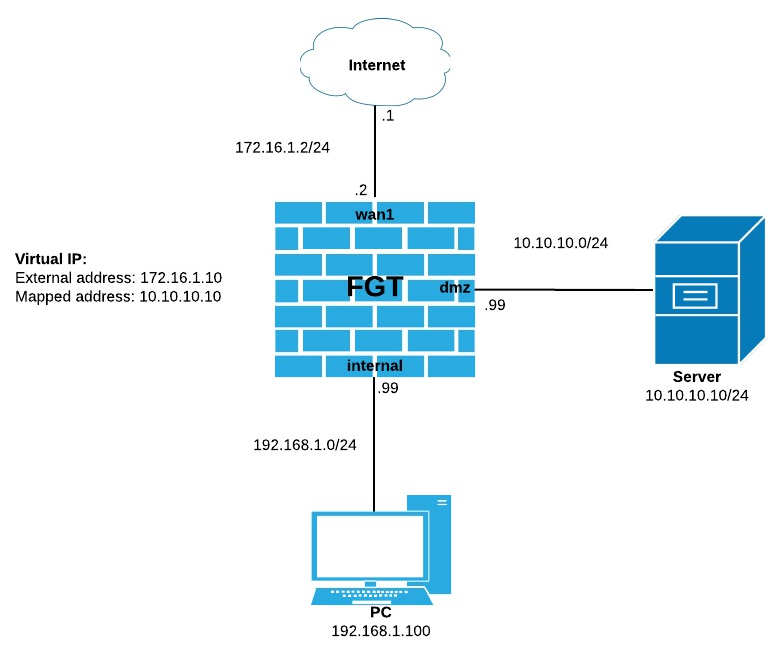
This article describes the configuration needed for Hairpin NAT.
Scenario: Internal user ("PC" in the follow diagram) needs to access Server (10.10.10.10)
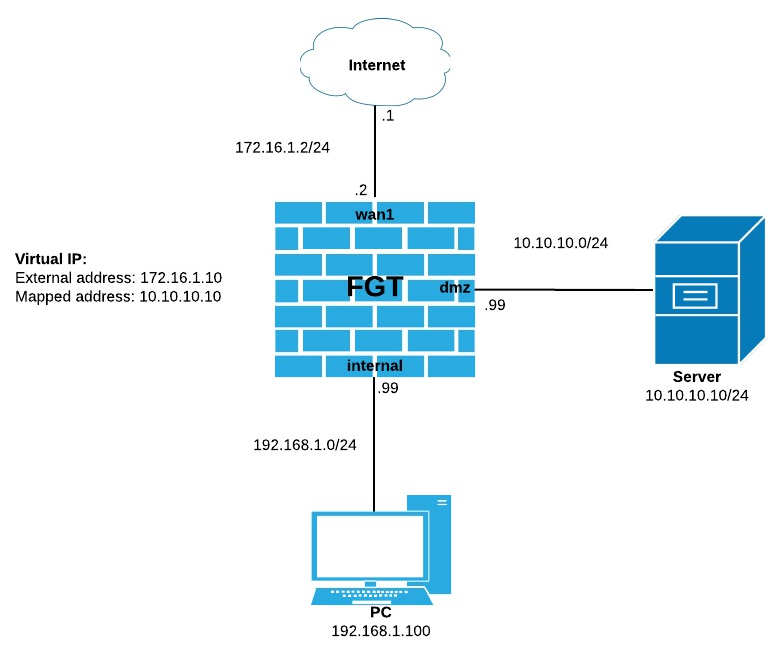
In this scenario, both PC and Server are behind FortiGate and PC wants to connect to Server by pointing to its external address (172.16.1.10) instead of its real one (10.10.10.10). This is called Hairpin NAT.
config firewall policy
edit 1
set srcintf "wan1"
set dstintf "dmz"
set srcaddr "all"
set dstaddr "VIP" <--- VIP object
set action accept
set schedule "always"
set service "ALL"
next
end
config firewall policy
edit 2
set srcintf "internal"
set dstintf "wan1" <-- Same as external interface defined in VIP
set srcaddr "all"
set dstaddr "all"
set action accept
set schedule "always"
set service "ALL"
set nat enable
next
end
config firewall policy
edit 3
set srcintf "internal"
set dstintf "dmz"
set srcaddr "all"
set dstaddr "VIP" <--- VIP object
set action accept
set schedule "always"
set service "ALL"
next
end
config firewall policy
edit 3
set srcintf "internal"
set dstintf "dmz"
set srcaddr "all"
set dstaddr "all"
set action accept
set schedule "always"
set service "ALL"
set match-vip enable
next
end
Article ID: 120
Created: Fri, Aug 4, 2017
Last Updated: Fri, Aug 4, 2017
Author: Les Carr
Online URL: https://kb2.ic.uk/article.php?id=120